什麼是汽車網路安全?
汽車網路安全是一種實務,在整個車輛生命週期中,保護機動車輛中使用或連接到機動車輛的所有電子系統,免受未經授權的存取、操縱、惡意修改或毀損。受保護的系統包括電子裝置、資料、網路、控制演算法和軟體。
自 1960 年代推出電子控制單元 (ECU) 起,網路安全挑戰也隨之出現。然而,自那時起,電動車 (EV)、混合動力系統、先進駕駛輔助系統 (ADAS)、智慧車輛系統和汽車產業連線能力的成長,也讓應對網路威脅成為優先事項。隨著軟體定義車輛 (SDV) 和半自動駕駛與全自動駕駛系統進入市場,這些疑慮急劇增加。
為什麼汽車生態系重視汽車網路安全
隨著車輛連線環境不斷演進,任何涉及汽車產業的公司都需要瞭解什麼是汽車網路安全,以及相關的威脅。如果他們直接涉及可能易受網路安全風險影響的元件,就需要遵守汽車網路安全標準中的準則。
主要的網路安全風險包括:
- 車輛系統控制:威脅行為者可以存取連網車輛中的 ECU,並控制轉向、煞車和加速等功能。
- 網路攻擊:駭客可能會利用常見的網路威脅,這些威脅通常與家用電腦、商業系統和現代車輛中的網路相關。阻斷服務 (DoS) 和勒索軟體攻擊是最常見的網路攻擊。
- 資料竊取:一旦惡意行為者取得車輛的存取權,他們就可以存取車輛資料,車主和乘客的資料也難逃毒手。資料竊取也包括即時存取道路車輛的位置。
- 實體進出:透過遙控鑰匙或行動應用程式解鎖汽車固然方便,但這種便利也讓駭客能夠實際進入車輛並安裝惡意軟體、破壞機械和電子系統,以及竊取物品或汽車本身。
- 遭入侵的人工智慧 (AI) 模型:愈來愈多的車輛系統 (包括 ADAS 和自動駕駛系統) 廣泛使用 AI 來解讀感測器輸出的資料、處理影像或控制車輛。網路犯罪分子可以存取 AI 模型,並插入可能導致 AI 系統輸出錯誤的惡意資料。
- 高電壓系統攻擊:在電動車和混合動力車中,由電池管理系統控制的高電壓和電流,是惡意行為者造成傷害的另一種途徑。他們使用 ECU 造成電池元件過熱,進而引發火災或爆炸。
存在網路安全漏洞的汽車資訊系統
幾乎每台現代車輛都包含某種電子元件充當資訊系統,容易遭到存取和入侵。從座椅加熱器到碰撞感測器,這些模組都讓網路安全工程面臨挑戰。此外,車內系統之間或與外部系統之間的任何連線,都存在工程師必須解決的網路威脅。
最常存在網路安全挑戰的汽車資訊系統包括:
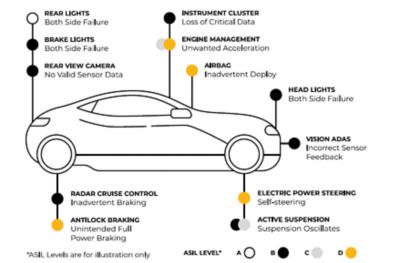
摘要說明現代車輛中一些最常見的智慧系統,以及適用於這些系統的自動化程度
汽車網路安全的產業標準
儘管與 ISO 26262 標準下的功能安全密切相關,並與之互補,但汽車網路安全的定義以及管理方式,自有一套國際標準。ISO/SAE 21434 網路安全風險管理標準涵蓋「道路車輛中電氣和電子 (E/E) 系統,包括其元件和介面的概念、產品開發、生產、營運、維護,以及除役。」
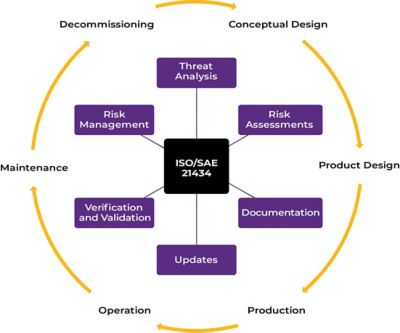
ISO/SAE 21434 汽車網路安全標準的關鍵層面
ISO/SAE 21434 標準不是規範解決方案,也不強制執行特定要求、技術或解決方案。相反,它提供流程導向的架構和準則,用於管理網路安全。本標準的關鍵層面包括:
- 涵蓋從概念設計到除役的整段車輛生命週期
- 使用威脅分析和風險評估 (TARA),採用風險式方法
- 建立組織網路安全管理系統 (CSMS)
- 將「考量安全的設計」整合至產品開發流程
- 在整個企業中,建立明確定義角色和責任的網路安全文化
- 致力於持續的網路安全活動
- 在汽車供應鏈的網路安全和管理方面進行協作
- 在網路安全和軟體更新兩方面,遵守聯合國歐洲經濟委員會 (UNECE) 的 UN R155 法規
- 將 V 形模型應用於軟體開發和系統設計
- 為所有網路安全活動和決策,導入可追溯性和文件記錄
- 為已上路使用的車輛定義明確的事故回應和漏洞管理流程
- 使用標準中定義的常見網路安全語言和術語
將網路安全有效整合至車輛開發生命週期
汽車供應鏈的原始設備製造商 (OEM) 和供應商都可以透過採用 ISO/SAE 21434 標準的以下建議,將網路安全措施有效整合至車輛開發生命週期。
整合分層方法以實現車輛網路安全
合規組織會在假設車輛子系統可能遭到入侵的情況下,建立分層方法。他們會制定措施來降低攻擊成功的可能性。當威脅行為者獲得未經授權的存取時,多層保護可將其造成的損害降至最低。
實作一般網路安全最佳實作範例
採用分層方法後,開發車輛控制系統的團隊應實作經過業界實證的最佳實作範例,盡可能消除風險,在設計中建立早期偵測並回應網路安全問題的功能,以及納入可實現快速復原的安全解決方案。此外,領導階層應在整個組織和供應鏈中優先考慮產品網路安全,並在所有利害關係人的協助下,開發和維護全面的網路安全管理系統。最後,團隊應與更廣泛的生態系統分享任何經驗教訓。
利用網路安全技術最佳實作範例
網路安全技術最佳實作範例的起點,是在設計流程初期使用威脅分析和風險評估工具。一旦團隊記錄威脅和風險,他們就可以部署特定的安全解決方案,例如限制存取車輛運算資源、使用加密技術、改善驗證流程,以及採用網路分段。接下來,隨著開發持續進行,工程師需要在生產前透過模擬和測試,設計並執行驗證和確認。生產後的其他活動包括繼續監控、建立和使用事件回應計畫,以及持續實作漏洞管理。
透過模擬提升汽車網路安全
從元件製造商到 OEM,汽車供應鏈的成員都會在產品生命週期的每個步驟使用模擬來引導設計、識別威脅、評估風險、確認解決方案以及驗證功能。模擬對網路安全的價值,與模擬對功能安全、效能、耐用性和效率的價值不相上下。
要瞭解模擬最有助於滿足哪些方面的特定網路安全需求,有種方法很實用,那就是查看車輛生命週期中一些較常見的工程任務。
產品概念設計
汽車網路安全標準強調,在任何車輛元件或系統的概念設計階段,都務必考量到網路安全。像 Ansys System Architecture Modeler (SAM) 這樣的工具非常適合視覺化、設計和管理複雜系統,每個步驟都能解決網路安全問題。在概念階段採用基於模型的系統工程 (MBSE) 方法,能為網路安全工程的每個部分帶來助益。
元件設計、硬體和軟體
一旦設計團隊進入元件設計階段,他們就可以利用模擬來調查並解決任何實體、電磁或軟體漏洞,然後再推進到實體原型階段。Ansys Maxwell 進階電磁場求解器和 Ansys HFSS 高頻電磁模擬軟體,可用於檢查網路或電子裝置中的訊號漏洞。在嵌入式系統的韌體軟體開發這方面,Ansys SCADE 嵌入式軟體產品組合內建網路安全功能,是標準型開發和測試解決方案的絕佳範例。另一種使用模擬來協助元件設計的重要方法,是使用 Ansys Optics 工具進行感測器設計、驗證和確認。
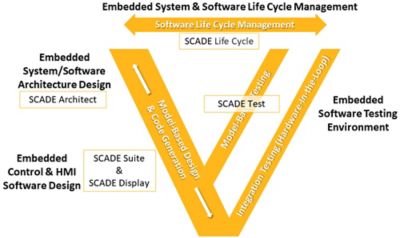
使用 Ansys SCADE 進行嵌入式系統和軟體生命週期管理的 V 形圖
系統設計與整合
電子、軟體和機械系統的整合特性,讓汽車系統設計和整合成為 MBSE 的理想應用領域。網路安全方面也不例外。供應商和 OEM 可以使用 Ansys ModelCenter 等基於模型的系統工程軟體工具,為系統建模以評估漏洞。此外,像 Ansys Medini Cybersecurity SE 等安全分析工具,非常適合將 TARA 當作設計流程的整合一環來執行。
網路安全測試
各行各業 (特別是汽車產業) 使用數位工程的比例日益提高,其中虛擬化測試的數量更是不斷增加。使用模擬來補充實體測試的目標,是以虛擬呈現取代昂貴且耗時的實驗室測試。對於網路安全而言,Ansys SCADE 軟體中的數位模型,出色示範如何並行且自動化進行滲透測試這類工作。
網路安全事件回應
當現場發生網路安全事件時,OEM 或供應商有責任瞭解事態如何,並提出解決方案。模擬工具是一種快速且有效的方法,可自動化調查流程並快速測試解決方案,而無需進行昂貴且耗時的實體測試。例如,Ansys Medini Cybersecurity SE 軟體透過其漏洞管理和監控功能,來支援這項工具。
相關資源
讓我們開始吧
如果您面臨工程挑戰,我們的團隊將隨時為您提供協助。憑藉豐富的經驗和對創新的承諾,我們邀請您與我們聯絡。讓我們共同合作,將您的工程障礙轉化為成長和成功的機會。立即與我們聯絡,開始對話。